Introduction
Scheduled tasks are widely used to automate operations on servers and endpoints. However, adversaries can exploit this feature to execute malicious payloads by retrieving them from external sources over HTTP or FTP. Detecting and mitigating these threats is critical to maintaining a secure environment.
The "Scheduled Task Created with HTTP or FTP Reference" playbook in the Cortex XSIAM® Response and Remediation Pack automates the investigation and response to such threats. By leveraging threat intelligence and automated remediation actions, this playbook helps prevent potential compromise from unauthorized scheduled task execution.
Threat Overview
Attackers often create scheduled tasks that reference remote servers to:
- Download and execute malicious scripts.
- Maintain persistence on compromised hosts.
- Evade security monitoring by utilizing external infrastructure.
This playbook is triggered when an alert is generated for a scheduled task containing an HTTP or FTP reference. It systematically analyzes, investigates, and remediates the detected threat.
Purpose of the Playbook
The "Scheduled Task Created with HTTP or FTP Reference" playbook follows a structured approach to identify and contain threats.
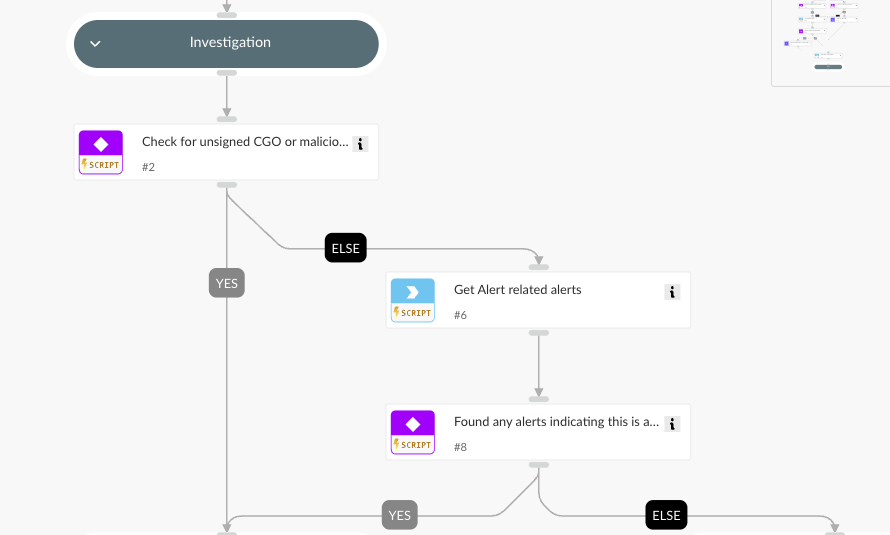
1. Investigationˇ
- Check the reputation of the referenced IP and URL using threat intelligence sources.
- Verifies the digital signature of the CGO process that created the task.
- Searches for related XSIAM alerts to determine if the scheduled task is part of a broader attack pattern.
2. Remediation
If any of the following conditions are met, the playbook initiates remediation:
- The CGO process is unsigned.
- The referenced IP or URL has a known malicious reputation.
- Related XSIAM alerts indicate malicious activity.
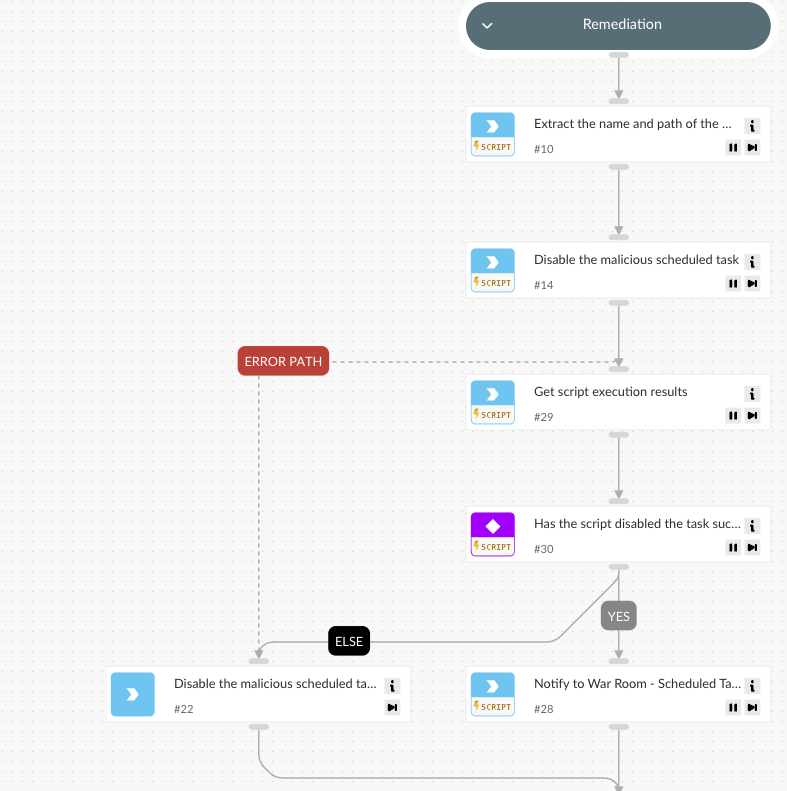
Remediation actions include:
- Disabling the scheduled task to prevent execution.
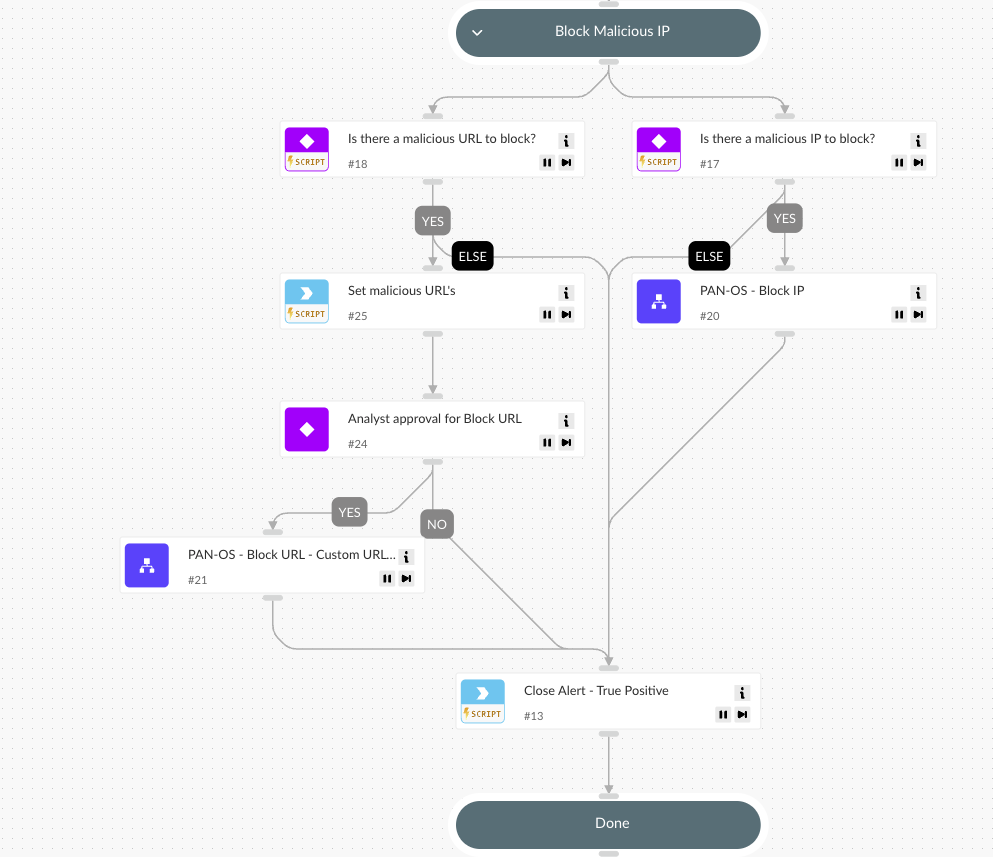
- Blocking the malicious IP and URL using Palo Alto Networks PAN-OS.
- Automatically closing the alert once remediation steps are completed.
Integration Requirements
To maximize the effectiveness of this playbook, organizations should integrate Cortex XSIAM with:
- Palo Alto Networks PAN-OS for automated URL and IP blocking.
Conclusion
The "Scheduled Task Created with HTTP or FTP Reference" playbook enhances security automation by swiftly detecting and mitigating threats associated with externally sourced scheduled tasks. By leveraging Cortex XSIAM’s advanced analytics, organizations can ensure proactive defense against unauthorized task execution and prevent potential breaches.
To deploy this playbook and see related automation use cases, visit the Cortex XSIAM Response and Remediation Pack.
To learn more about how you can transform your SOC through automation, schedule a personal demo for Cortex XSIAM.